- Joined
- May 15, 2008
- Messages
- 83
- Reaction score
- 0
INTRODUCTION:
(Afterwards, the actual steps to perform beyond CIS Tool suggestions (which will need you to use tools like secpol.msc, gpedit.msc, services.msc, regedit.exe, explorer.exe + more, yet, all native tools to your OS) will be listed for your reference, each in their own post reply, to avoid "clutter"):
Windows CAN be secured very well, but, you have to go thru some "GYRATIONS/EFFORT" to do it, but, it IS doable (but not to any 100% levels, because again - new holes/vulnerabilities appear in the OS & its libs + apps, but this gets you closer, if not as close as a body needs to be!).
THIS IS GEARED TO "stand-alone" systems online on the internet (However - it can be adapted for LAN/WAN office or home networked environs, BUT, pay attention to step #2's 'warnings' about pulling Client For Microsoft Networks, &/or File & printer sharing - most networks require/need this)
--------------------------------------------------------------------------------------------------------------
BACKGROUND & INFORMATION + TOOLS YOU CAN USE TO HELP YOU SECURE YOUR SYSTEM:
--------------------------------------------------------------------------------------------------------------
Here I am running Windows Server 2003 SP #2, fully current patched by MS update pages, here (I check it every 2nd Tuesday of the month of course, on "Patch Tuesday's"):
http://www.microsoft.com/downloads/...ryid=7&sortCriteria=date&sortOrder=descending
It is a personally 'security-hardened' model I have been working on for many years, using principals I learned & used since the NT 3.5x days onward to this version of the OS: As is now?
I score an 85.760 on the CIS Tool 1.x currently as of 10/10/2007!
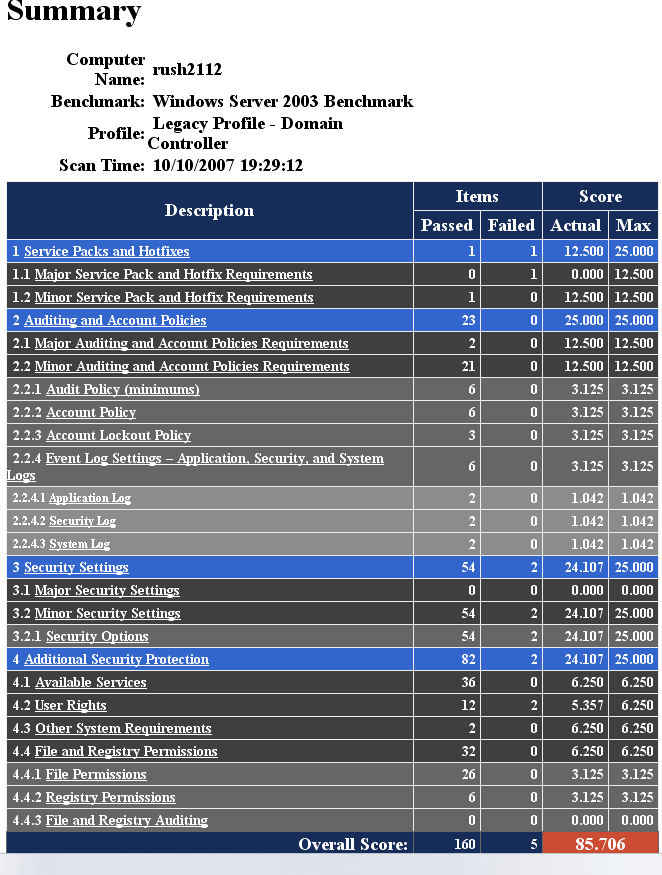
This is up from my past score here of 76.xxx on it (default score I had prior to this security hardening via CIS TOOL & its advisements & past the 84.735 I initially hardened it up to, & later 85.185 as well), & here is how to do it!
Currently, I can go NO higher than this score of 85.760 (of 100 total) on CIS Tool 1.x for Windows, pictured here (photo proof/pictures DO say, a 1,000 words (like this post, lol)) & even IF I could get past the few areas I know are wrong (the test errs, as it does on some areas in LINUX as well), I cannot get past 88% or so, period!
============================================================================
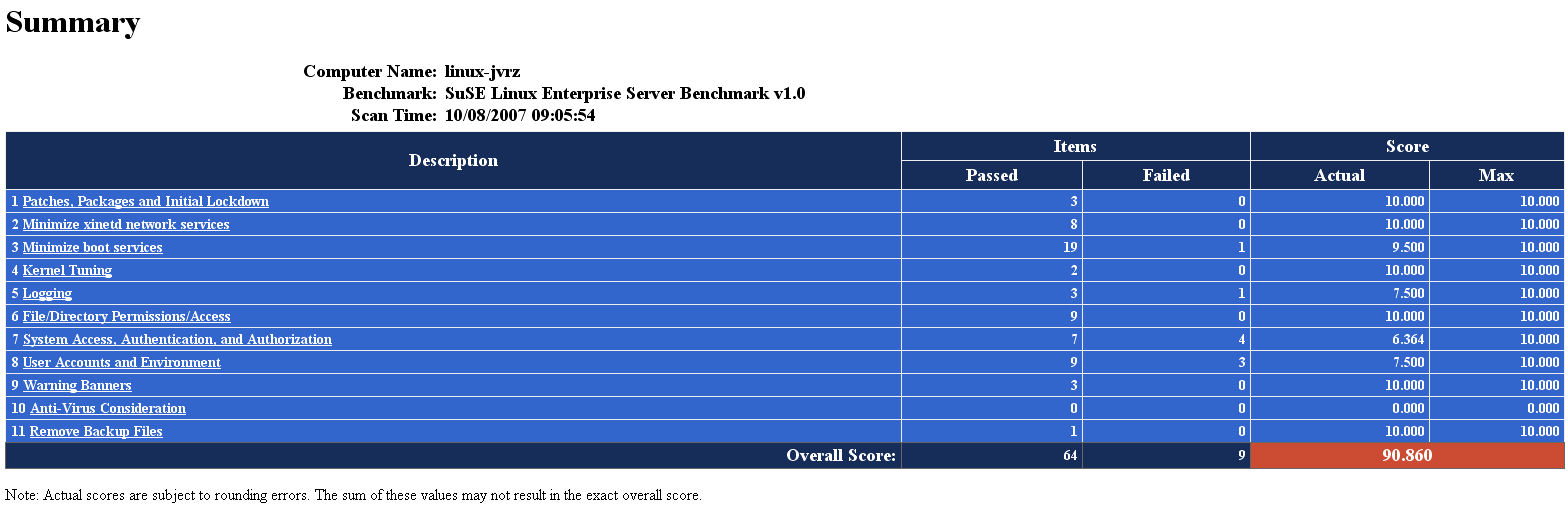
HERE ARE LINUX SCORES FROM CIS TOOL (SuSE Enterprise Linux under VMWare):
============================================================================
HARDENED LINUX:
DEFAULT LINUX:
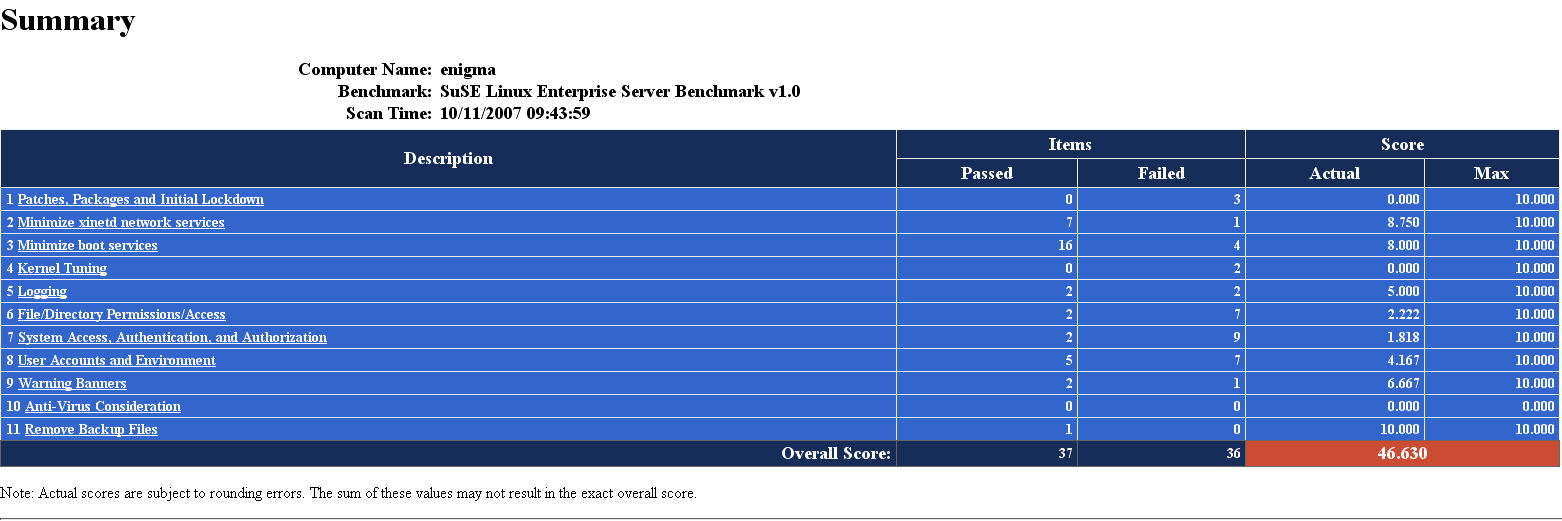
(It appears that LINUX has FAR LESS TESTED, when compared to the SIZE of the Windows tets, & Linux CAN reach 90++ scores (but there is an error in CIS TOOL preventing myself from going to a higher than 85.760 score & I have submitted the data to CIS TOOL's authors on that account WITH PROOFS, and even if I could get the few areas I am scored down on still, it would not add to past 88% or so... bug, bigtime, do the math from my score & see))
============================================================================
That is a DECENT ENOUGH score (especially considering the default score of VISTA even, is FAR BELOW THAT! Nice part is? The techniques noted here can LARGELY APPLY TO VISTA AS WELL, but afaik there is no CIS Tool version for VISTA (yet)! Still, read on...)
(For CIS Tool - There are Linux, Solaris, BSD variants, & other OS models ports (some only in .pdf security guide form though, not programmatically automated yet, like MacOS X) of this are available too by the way - not really "ports" strictly speaking, they require JAVA to run)
-------------------------------------------------------------------------------------------------------------------
DOWNLOAD URL FOR CIS TOOL (for multiple platforms), from "The Center for Internet Security" here:
-------------------------------------------------------------------------------------------------------------------
http://www.cisecurity.org/bench.html
IMPORTANT: This tool IS invaluable in guiding you to a more secure OS, on any OS platform really!
It actually makes it "FUN", in a techie/geeky/nerdy (whatever) kind of way, in that you really find out WHAT it is you know, vs. the CIS Tool results, as far as securing a Windows NT-based system. E.G./I.E,-> I've been @ this field in a professional capacity since 1994, & it taught me a "trick-or-two", let's put it THAT way.
CIS Tool = Great stuff, that makes much of this easier (what I add ontop of it is in the next steps)!
APK
P.S.=> Now that the "introductory material" (tools to use, how/why, results possible, etc. et al) has been put down? Now, here we go to the actual "meat" of the subject in my next post(s).
Also - IF you have more to add to this, OR critique of my points? Please - have @ it & let 'em rip (as we ALL can gain by for security & peace-of-mind online hopefully)
HOWEVER, please - hold off on the "English Grammar" critiques + "writing style" comments if you have those (I did my best + refine it as I go & add more)
I would try to have made it shorter too, but it's complex material @ times, & definitely a lot of it (CIS Tool helps though)!
(So please, as to critiques - I only ask that you keep it computer security technically oriented, adding points I may have missed or supplementing those I suggest with alternates to things I Have).
Thanks & enjoy! apk
(Afterwards, the actual steps to perform beyond CIS Tool suggestions (which will need you to use tools like secpol.msc, gpedit.msc, services.msc, regedit.exe, explorer.exe + more, yet, all native tools to your OS) will be listed for your reference, each in their own post reply, to avoid "clutter"):
Windows CAN be secured very well, but, you have to go thru some "GYRATIONS/EFFORT" to do it, but, it IS doable (but not to any 100% levels, because again - new holes/vulnerabilities appear in the OS & its libs + apps, but this gets you closer, if not as close as a body needs to be!).
THIS IS GEARED TO "stand-alone" systems online on the internet (However - it can be adapted for LAN/WAN office or home networked environs, BUT, pay attention to step #2's 'warnings' about pulling Client For Microsoft Networks, &/or File & printer sharing - most networks require/need this)
--------------------------------------------------------------------------------------------------------------
BACKGROUND & INFORMATION + TOOLS YOU CAN USE TO HELP YOU SECURE YOUR SYSTEM:
--------------------------------------------------------------------------------------------------------------
Here I am running Windows Server 2003 SP #2, fully current patched by MS update pages, here (I check it every 2nd Tuesday of the month of course, on "Patch Tuesday's"):
http://www.microsoft.com/downloads/...ryid=7&sortCriteria=date&sortOrder=descending
It is a personally 'security-hardened' model I have been working on for many years, using principals I learned & used since the NT 3.5x days onward to this version of the OS: As is now?
I score an 85.760 on the CIS Tool 1.x currently as of 10/10/2007!
This is up from my past score here of 76.xxx on it (default score I had prior to this security hardening via CIS TOOL & its advisements & past the 84.735 I initially hardened it up to, & later 85.185 as well), & here is how to do it!
Currently, I can go NO higher than this score of 85.760 (of 100 total) on CIS Tool 1.x for Windows, pictured here (photo proof/pictures DO say, a 1,000 words (like this post, lol)) & even IF I could get past the few areas I know are wrong (the test errs, as it does on some areas in LINUX as well), I cannot get past 88% or so, period!
============================================================================
HERE ARE LINUX SCORES FROM CIS TOOL (SuSE Enterprise Linux under VMWare):
============================================================================
HARDENED LINUX:
DEFAULT LINUX:
(It appears that LINUX has FAR LESS TESTED, when compared to the SIZE of the Windows tets, & Linux CAN reach 90++ scores (but there is an error in CIS TOOL preventing myself from going to a higher than 85.760 score & I have submitted the data to CIS TOOL's authors on that account WITH PROOFS, and even if I could get the few areas I am scored down on still, it would not add to past 88% or so... bug, bigtime, do the math from my score & see))
============================================================================
That is a DECENT ENOUGH score (especially considering the default score of VISTA even, is FAR BELOW THAT! Nice part is? The techniques noted here can LARGELY APPLY TO VISTA AS WELL, but afaik there is no CIS Tool version for VISTA (yet)! Still, read on...)
(For CIS Tool - There are Linux, Solaris, BSD variants, & other OS models ports (some only in .pdf security guide form though, not programmatically automated yet, like MacOS X) of this are available too by the way - not really "ports" strictly speaking, they require JAVA to run)
-------------------------------------------------------------------------------------------------------------------
DOWNLOAD URL FOR CIS TOOL (for multiple platforms), from "The Center for Internet Security" here:
-------------------------------------------------------------------------------------------------------------------
http://www.cisecurity.org/bench.html
IMPORTANT: This tool IS invaluable in guiding you to a more secure OS, on any OS platform really!
It actually makes it "FUN", in a techie/geeky/nerdy (whatever) kind of way, in that you really find out WHAT it is you know, vs. the CIS Tool results, as far as securing a Windows NT-based system. E.G./I.E,-> I've been @ this field in a professional capacity since 1994, & it taught me a "trick-or-two", let's put it THAT way.
CIS Tool = Great stuff, that makes much of this easier (what I add ontop of it is in the next steps)!
APK
P.S.=> Now that the "introductory material" (tools to use, how/why, results possible, etc. et al) has been put down? Now, here we go to the actual "meat" of the subject in my next post(s).
Also - IF you have more to add to this, OR critique of my points? Please - have @ it & let 'em rip (as we ALL can gain by for security & peace-of-mind online hopefully)
HOWEVER, please - hold off on the "English Grammar" critiques + "writing style" comments if you have those (I did my best + refine it as I go & add more)
I would try to have made it shorter too, but it's complex material @ times, & definitely a lot of it (CIS Tool helps though)!
(So please, as to critiques - I only ask that you keep it computer security technically oriented, adding points I may have missed or supplementing those I suggest with alternates to things I Have).
Thanks & enjoy! apk

